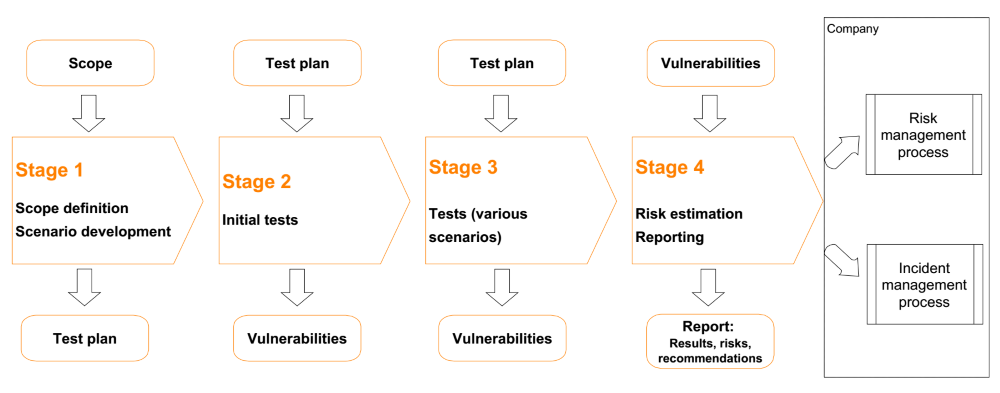
The aim of the tests is to check the employees’ security awareness by conducting comprehensive attempts to obtain confidential information (e.g. phishing, phone calls or entry on the company premises) or attempts to persuade personnel to engage in activities which contradict the principles of security (e.g. through phishing). The tests are performed by experienced, professional security engineers, who hold numerous certificates, such as CEH, CPTE, OSCP, OSCE, and who have experience in the scope of system security, system administration and software development. Test results serve as a point of reference for managing risks and security incidents at the organisation. We have conducted such tests for banks, brokerages, leasing companies, energy providers, telecommunications service providers, producers, e-commerce businesses and others. More information can be found at http://optimapartners.pl/pl/projekty/projekty.
Benefits:
- Increasing the level of security of data processed in IT systems.
- Minimising the risk of security breaches and successful cyberattacks.
- Detecting current vulnerabilities, loopholes, errors in software and systems before they are detected by cybercriminals.
- Practical, implementable and cost-efficient recommendations (quick wins).
- Compliance with international norms and standards (ISO 27001, OWASP, OSSTMM, PCI DSS).
- Avoiding financial losses, reputational damage and legal consequences.
Approach
Test scenarios
- Phishing (e.g. sending e-mails with a link to malicious software).
- Phone calls to employees to obtain confidential information.
- Bringing data carriers to the company premises (e.g. pendrives) containing malicious software.
- Entering the company premises to obtain confidential information.
- Establishing a false Wi-Fi network.
Reports The results of our work are described in detail in a report, which usually consists of the following sections:
- Summary
- Detailed results, including:
- Aim
- Scope
- Approach, methods and tools
- Identified vulnerabilities
- Vulnerability detection method
- Evidence of vulnerabilities
- Security breach risk
- Recommendations
Test results are presented in detail and discussed during meetings with the client.
Recommendation deployment
In addition, we offer support with implementation of our recommendations, access to our security engineers and databases of information about vulnerabilities and ways of eliminating them.
